Malware
“Unveiled: The Infamous BlackCat Ransomware Gang Responsible for the Devastating February Reddit Breach”
The Blackcat ransomware gang is believed to be behind the February breach of Reddit, where hackers accessed some of the site’s systems and stole data. The group is known for using double extortion tactics, where they threaten to release stolen data if a ransom is not paid. The FBI is currently investigating the incident and urging Reddit users to change their passwords.

Is there a Connection Between the Infostealer Malware and the BlackCat Ransomware Gang?
Recent cybersecurity reports suggest a potential link between the Infostealer malware and the notorious BlackCat Ransomware Gang. It is believed that the gang may have gained access to over 100k chatgpt accounts breached, using this valuable information to launch their ransomware attacks. The connection between these two threats signifies a worrisome collaboration in the cybercrime landscape, emphasizing the need for enhanced security measures.
BlackCat Ransomware Gang Claims Responsibility for Reddit Cyberattack
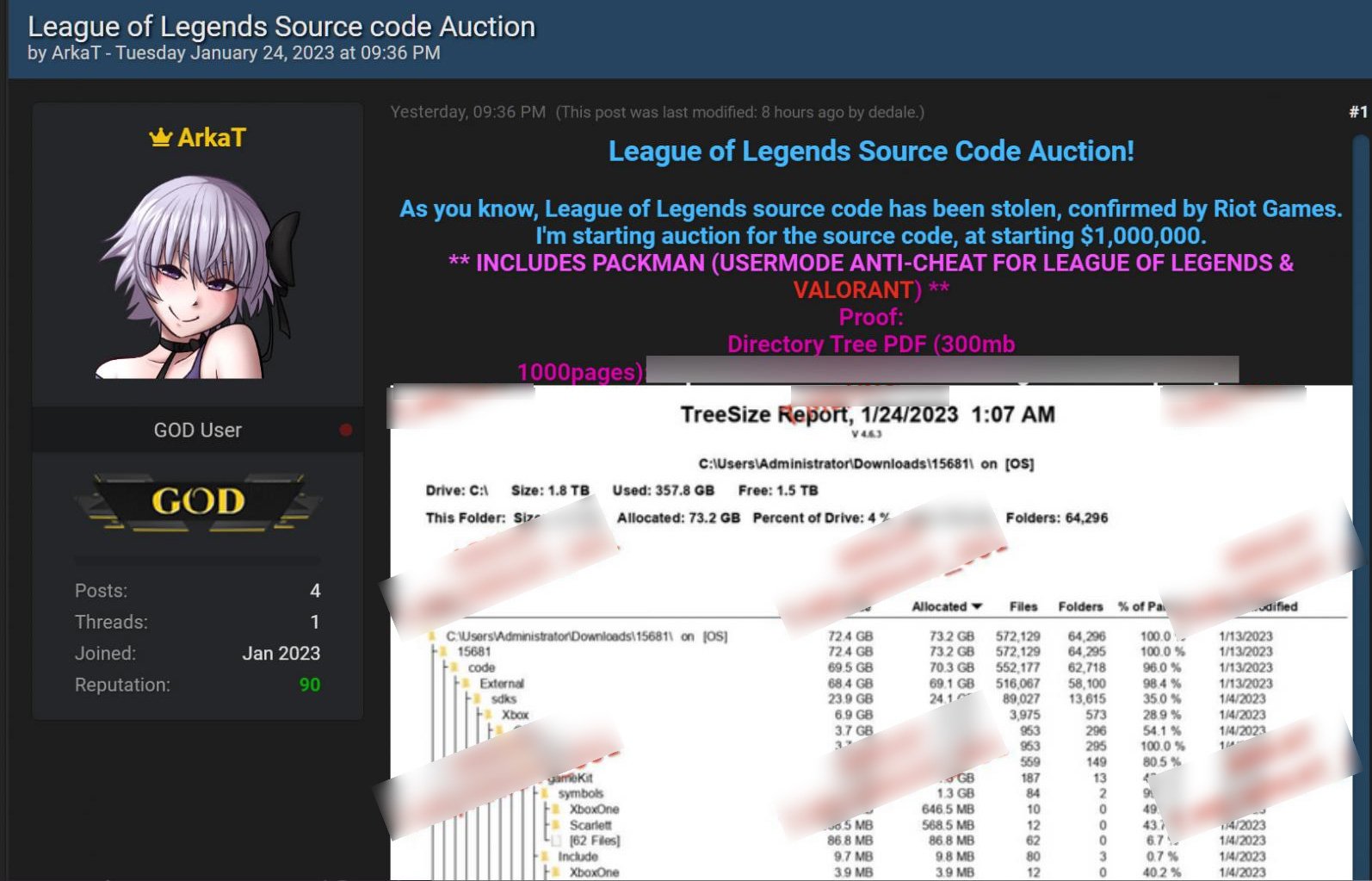
Reddit suffered a cyberattack in February, where the BlackCat (ALPHV) ransomware gang stole 80GB of data from the company. On February 9th, Reddit revealed that its systems were breached on February 5th, when an employee was tricked into a phishing attack. The attackers gained access to Reddit’s systems and stole internal documents, source code, employee data, and limited data about the company’s advertisers. According to Reddit CTO Christopher Slowe (KeyserSosa), the attacker obtained access to some internal documentation, code, and internal dashboards and business systems after obtaining a single employee’s credentials. Although no breach was found in Reddit’s primary production systems that store the majority of its data and run Reddit, the company said that it was a phishing attack similar to one on Riot Games that allowed hackers to gain access to systems and steal source code for League of Legends (LoL), Teamfight Tactics (TFT), and the company’s Packman legacy anti-cheat platform. Riot Games was asked to pay $10 million to stop the data leak, but when it refused, the threat actors attempted to sell the data for $1 million on a hacking forum.
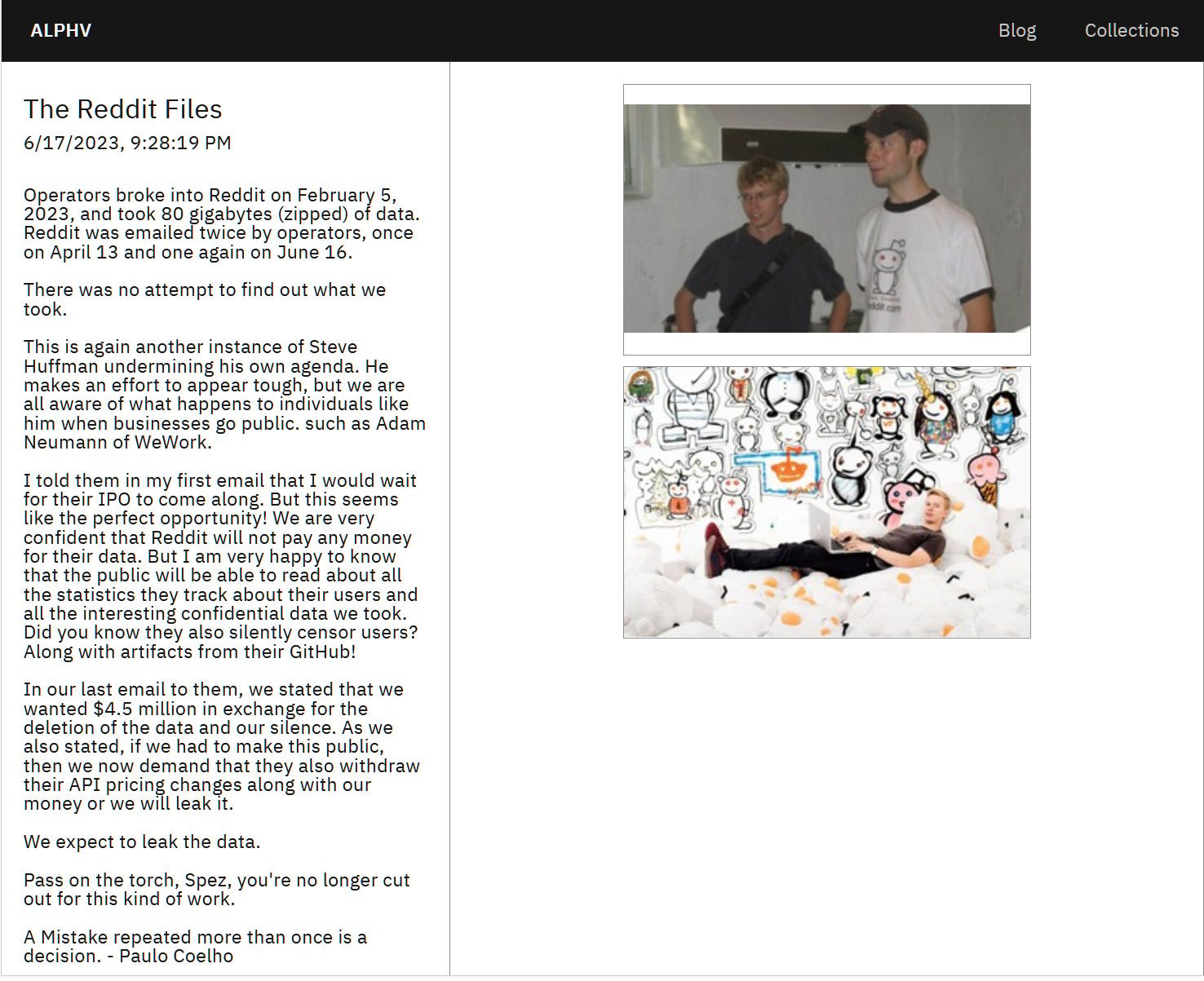
Source: BleepingComputer
BlackCat, also known as ALPHV ransomware operation, has claimed responsibility for the Reddit cyberattack. As per the threat actors, they have stolen 80 GB of compressed data from the company during the attack and plan to leak the data. BlackCat claims that it attempted to contact Reddit twice, on April 13th and June 16th, demanding $4.5 million for deleting the data, but it did not receive a response. The ransomware operation threatened Reddit, saying that it was very confident that the company would not pay any money for their data. BlackCat is happy that the public will be able to read about all the statistics that Reddit tracks about its users and all the confidential data that the attackers took. The group also claimed that Reddit silently censors users, along with artifacts from their GitHub. Reddit declined to comment on BlackCat’s post, but BleepingComputer has confirmed that this is the same attack disclosed by Reddit in February.
Source: BleepingComputer
The same hacking group that attacked Reddit is believed to be responsible for a similar attack on Western Digital in March 2023, which caused a massive outage to the company’s My Cloud cloud service. Although at first, the threat actors claimed not to have a name, screenshots of the stolen data were leaked on the ALPHV data leak site, with the attackers taunting the company about the attack. Western Digital sent data breach notifications in May, warning online store customers that their data was stolen during the attack.
Malware
Finastra Battles Massive Data Breach: Unraveling the SFTP Hack Impact on Fintech Titan
Fintech firm Finastra is probing a potential data breach following a hacking incident involving its SFTP server. The breach, which may have exposed sensitive user data, has prompted the company to bolster its security measures and notify affected customers.

Did you know that even the largest and most successful financial software companies can fall victim to cyberattacks? Recently, Finastra, a company that serves over 8,000 institutions across 130 countries, experienced a cybersecurity incident that put their customers’ sensitive data at risk.
The Incident at Finastra
Finastra is a global financial software company that counts 45 of the world’s top 50 banks and credit unions among its clients. With over 12,000 employees and a revenue of $1.7 billion last year, it’s a major player in the finance sector. On November 7, 2024, a cyber attacker managed to access one of Finastra’s Secure File Transfer Platform (SFTP) systems using compromised credentials.
So far, the company’s investigation, supported by external cybersecurity experts, has not found evidence that the breach extended beyond the SFTP platform. But the attack has raised concerns about the security of the company’s software services, which include lending solutions, payment processing, cloud-enabled retail and banking platforms, and trading risk management tools.
How We Learned About the Breach
Brian Krebs first reported the security breach after seeing a data breach notification sent to an impacted person. The attack appears to be linked to a post on a hacking forum, where a threat actor named “abyss0” claimed to be selling 400GB of data stolen from Finastra.
When we asked Finastra about the forum post, they wouldn’t confirm or deny if the data belonged to them. However, they did acknowledge a limited-scope security breach and are currently evaluating its impact. They also stressed that the compromised SFTP platform was not used by all their customers and was not their default file exchange platform.
What’s Next for Finastra and Its Customers?
The exact impact and scope of the breach are still under investigation. It may take some time to determine who has been affected, but Finastra has assured that those who are deemed impacted will be contacted directly. As a result, public disclosures from the company are not expected.
Interestingly, the threat actor who published the data samples earlier this month has since deleted the post. It’s unclear whether the data was sold to a buyer or if “abyss0” became concerned about the sudden publicity.
A History of Cybersecurity Incidents
This isn’t the first time Finastra has experienced a cybersecurity incident. In March 2020, the company was hit by ransomware actors and forced to take parts of its IT infrastructure offline, causing service disruptions. At the time, reports highlighted Finastra’s lackluster vulnerability management strategy, as they were using older versions of Pulse Secure VPN and Citrix servers.
What Can We Learn From This?
The Finastra breach is a stark reminder that no organization is immune to cyber threats. As technology continues to evolve, so do the tactics and techniques used by cybercriminals. It’s crucial for companies, large and small, to prioritize cybersecurity and invest in the latest security measures to protect their customers’ data.
And for you, as a reader and potential customer, it’s important to stay informed about the latest cybersecurity news and best practices. That’s where we come in. We’re committed to providing you with the most up-to-date information on cybersecurity, so you can stay one step ahead of the bad guys. So why not reach out to us and keep coming back to learn more about how you can protect yourself and your business from cyber threats?
Malware
Ford Dismisses Data Breach Accusations, Asserts Customer Information Remains Secure
Ford has denied allegations of a data breach, assuring customers that their information remains secure. The automaker responded to claims made by a security researcher who discovered a vulnerability in their systems, stating that no sensitive data was accessed or exposed. Ford is working closely with the researcher to investigate and resolve the issue.

As someone who cares about cybersecurity, I can’t help but feel concerned about the recent news that Ford is investigating allegations of a data breach. A threat actor going by the name ‘EnergyWeaponUser’ claimed on a hacking forum to have leaked 44,000 customer records. They also implicated another hacker, ‘IntelBroker,’ who supposedly took part in the breach back in November 2024.
What’s in the leaked data?
The leaked information includes Ford customer records containing personal details such as full names, physical locations, purchase details, dealer information, and record timestamps. While this data might not be extremely sensitive, it still contains personally identifiable information (PII) that could be used in phishing and social engineering attacks targeting the affected individuals.
What’s interesting is that the threat actors didn’t try to sell the dataset. Instead, they offered it to registered members of the hacker forum for eight credits, equivalent to just a little over $2.
Ford’s response and investigation
We reached out to Ford to validate the claims, and a spokesperson confirmed that they are actively investigating the allegations. They stated, “Ford is aware and is actively investigating the allegations that there has been a breach of Ford data. Our investigation is active and ongoing.”
Is there credibility to these allegations?
The involvement of IntelBroker in the breach lends some credibility to the threat actor’s allegations. This hacker has a track record of confirmed breaches, including recent ones at Cisco’s DevHub portal, Nokia (through a third party), Europol’s EPE web portal, and T-Mobile (via a vendor).
The data samples leaked by the threat actors include locations from around the world, with the United States being one of them.
How to protect yourself from potential risks
In light of this potential data exposure, it’s crucial to treat unsolicited communications with caution and reject requests for revealing more information under any pretense. Keep an eye out for any suspicious emails, messages, or phone calls that might use this leaked information to manipulate or deceive you.
An important update from Ford
After our initial report, Ford provided us with an additional statement based on new findings from their ongoing investigation. They said, “Ford’s investigation has determined that there was no breach of Ford’s systems or customer data. The matter involved a third-party supplier and a small batch of publicly available dealers’ business addresses. It is our understanding that the matter has now been resolved.” – A Ford spokesperson
Stay informed and stay safe
Keeping up to date with cybersecurity news and best practices is crucial in today’s digital world. Continue to check back with us for the latest information and advice on protecting yourself and your data. Remember, knowledge is power, and staying informed is the first step in defending against potential threats.
Malware
US Space Tech Powerhouse Maxar Reveals Massive Employee Data Breach
US-based space technology firm Maxar Technologies has disclosed a data breach, potentially affecting current and former employees. The company discovered unauthorized access to its database, which may have exposed personal information such as names, birth dates, and Social Security numbers. Maxar has launched an investigation and is offering identity theft protection services to affected individuals.

Picture this: You work at a leading U.S. satellite maker, Maxar Space Systems, and one day, out of the blue, you receive a notification that hackers have accessed your personal data. It’s a nightmare scenario, right? Well, that’s exactly what happened to some employees at Maxar.
Breaking into Maxar’s Network
Maxar discovered that a hacker had breached their company network and accessed files containing employee personal data. The intruder used a Hong Kong-based IP address and had access to the system for about a week before the company discovered the breach.
As soon as Maxar’s information security team detected the unauthorized access, they took action to prevent the hackers from going deeper into the system. But the damage was already done.
Why You Should Care About Maxar
Maxar Space Systems is a big deal in the American aerospace industry. They’re known for building communication and Earth observation satellites. Based in Colorado, they have built more than 80 satellites currently in orbit. Their technology plays a significant role in space exploration, like the Maxar 1300 platform’s essential role in NASA’s Psyche mission and the power and propulsion elements used for the Artemis Moon exploration program.
What Personal Data Was Exposed?
The hacker likely accessed the following employee information:
- Name
- Home address
- Social security number
- Business contact information
- Gender
- Employment status
- Employee number
- Job title
- Hire/termination and role start dates
- Supervisor
- Department
Thankfully, no bank account information was exposed in this cybersecurity incident.
What’s Next for Maxar Employees?
Maxar is offering affected current employees IDShield identity protection and credit monitoring services. Former employees have until mid-February 2025 to enroll in identity theft protection services from IDX.
While the data breach exposed personal information, it’s also important to consider the potential impact on proprietary technical data. In a somewhat related incident, a threat actor claimed in July to have scraped the user base of GeoHIVE, a geospatial intelligence platform by Maxar Technologies, the parent company of Maxar Space Systems.
We reached out to Maxar Technologies to ask about the possibility of confidential technology data exposure and a possible link to the scraping incident, but a comment wasn’t immediately available.
Take Action to Protect Yourself
This breach at Maxar Space Systems is a stark reminder of the importance of cybersecurity. Don’t wait until it’s too late to protect your personal and business data. If you’re not sure where to start, we’re here to help. Our IT Services will guide you through the process of securing your data and keeping it safe from hackers.
Contact us today and stay ahead of the game. And don’t forget to keep coming back to learn more about cybersecurity and how you can protect yourself and your business.
-

 Malware1 year ago
Malware1 year agoFlagstar Bank’s Latest Data Breach: 800,000 Customers Impacted, Marking the Third Incident of 2021
-

 Malware1 year ago
Malware1 year agoBlackbaud: Taking Responsibility with a Landmark $49.5 Million Settlement for Devastating Ransomware Data Breach
-

 Data Protection Regulations1 year ago
Data Protection Regulations1 year agoTop Data Protection Officer Certification Courses Reviewed
-

 Security Audits and Assessments1 year ago
Security Audits and Assessments1 year agoMastering Healthcare Data Security: 5 Essential Audit Tips
-

 Data Protection Regulations1 year ago
Data Protection Regulations1 year agoTop 11 Data Protection Training Programs for Compliance
-

 Data Protection Regulations1 year ago
Data Protection Regulations1 year agoNavigating Data Protection Laws for Nonprofits
-

 Data Protection Regulations1 year ago
Data Protection Regulations1 year ago9 Best Insights: CCPA’s Influence on Data Security
-

 Security Audits and Assessments1 year ago
Security Audits and Assessments1 year agoHIPAA Security Risk Assessment: Essential Steps Checklist




























