Malware
Breaking News: Massive Info-Stealing Malware Breach Exposes Over 400,000 Corporate Credentials
Over 400,000 corporate credentials have been compromised by a potent information-stealing malware, affecting companies worldwide. This malware, named “SystemBC,” targets Windows systems and is used to gain unauthorized access to sensitive data, including login credentials and financial details. Organizations are urged to stay vigilant, update their security measures, and ensure strong password protocols to protect against potential cyber threats.

How Did the Hackers Gain Access to iOttie’s Site and Steal Credit Card Information?
A credit card data breach at iottie recently occurred when hackers found a way to gain unauthorized access to the site. This unfortunate incident allowed them to steal valuable credit card information from unsuspecting customers. The breach raises concerns about iOttie’s security measures and highlights the need for heightened security protocols to safeguard personal information from such threats.
Is there a connection between the AP Stylebook data breach and the info-stealing malware breach?
The massive ap stylebook breach fuels phishing concerns, raising questions about its connection to the info-stealing malware breach. Both incidents highlight the vulnerability of sensitive data and underscore the need for heightened cybersecurity measures. Ensuring robust protections and staying vigilant against evolving cyber threats is crucial in safeguarding against such breaches.
Data Theft: A Significant Threat to Business Environments
Recent analysis of nearly 20 million logs of information-stealing malware sold on the dark web and Telegram channels has revealed the alarming extent of infiltration into business environments.
Information stealers are a type of malware designed to pilfer data from various applications, including web browsers, email clients, instant messengers, cryptocurrency wallets, FTP clients, and gaming services. The stolen data is then packaged into archives known as “logs,” which are either used by threat actors for attacks or sold on cybercrime marketplaces.
The most notable families of information stealers, namely Redline, Raccoon, Titan, Aurora, and Vidar, are offered to cybercriminals through a subscription-based model. This allows them to conduct targeted malware campaigns and extract data from infected devices.
While information stealers primarily target careless internet users who download software from unreliable sources, it has become evident that they pose a significant threat to corporate environments as well.
This is due to employees using their personal devices for work or accessing personal content from work computers, resulting in numerous infections that lead to the theft of business credentials and authentication cookies.
A recent report by cybersecurity firm Flare, shared with IT Services, details the presence of approximately 375,000 logs containing access to various business applications such as Salesforce, Hubspot, Quickbooks, AWS, GCP, Okta, and DocuSign[1].
Specifically, Flare’s analysis of the stealer logs revealed:
- 179,000 AWS Console credentials
- 2,300 Google Cloud credentials
- 64,500 DocuSign credentials
- 15,500 QuickBooks credentials
- 23,000 Salesforce credentials
- 66,000 CRM credentials
In addition, there are approximately 48,000 logs that include access to “okta.com,” an enterprise-grade identity management service used by organizations for user authentication across cloud and on-premise platforms.
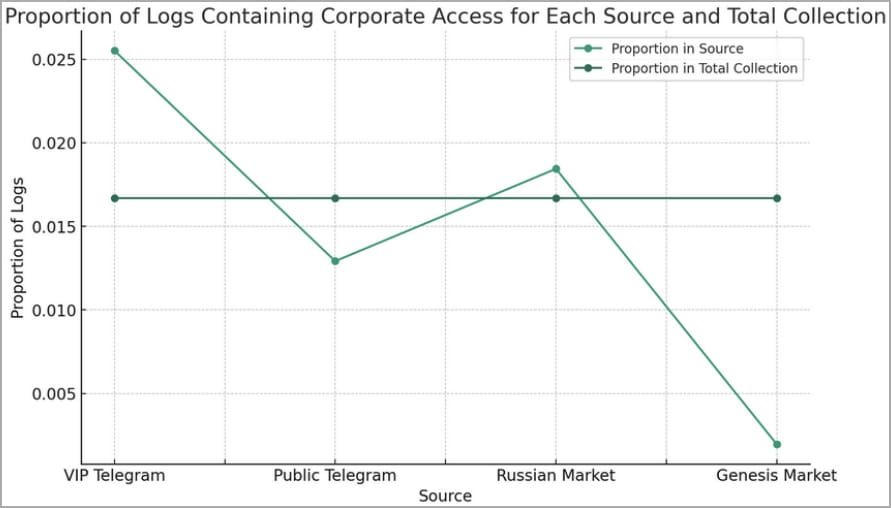
Of all the logs, 74% were found on Telegram channels, while 25% were discovered on Russian-speaking marketplaces such as the “Russian Market.”[1]
The Flare report suggests that the over-representation of logs containing corporate access on Russian Market and VIP Telegram channels indicates a deliberate or incidental focus on targeting corporate entities. Public Telegram channels may intentionally post lower-value logs, reserving high-value logs for paying customers[1].
Furthermore, Flare discovered over 200,000 stealer logs containing OpenAI credentials, twice the amount reported by Group-IB recently. This poses a significant risk of leaking proprietary information, internal business strategies, source code, and more[1].
Corporate credentials, known as “tier-1” logs, are highly valued in the cybercrime underground. They are sold on private Telegram channels or forums like Exploit and XSS. Cybercriminals can leverage compromised credentials to gain access to CRMs, RDP, VPNs, and SaaS applications, and then deploy stealthy backdoors, ransomware, and other malicious payloads[1].
Flare researcher Eric Clay explains that evidence from the dark web forum Exploit suggests that initial access brokers use stealer logs as a primary source to gain a foothold in corporate environments, which can then be auctioned off on top-tier dark web forums[1].
To minimize the risk of info-stealer malware infections, it is highly recommended that businesses enforce the use of password managers, implement multi-factor authentication, and establish strict controls on personal device usage. Additionally, employees should undergo training to identify and avoid common infection channels, such as malicious Google Ads, YouTube videos, and Facebook posts.
Sources:
Malware
USDoD Hacker Responsible for Massive National Public Data Breach Captured in Brazil
Brazilian authorities have arrested a hacker accused of stealing 223GB of sensitive data from the US Department of Defense (DoD). The hacker, known as “Zambrius,” sold the data on the dark web and was also involved in other cybercrimes.

Imagine waking up one day to find your personal information plastered all over the internet. Well, that nightmare became a reality for millions of Americans when notorious hacker USDoD, also known as EquationCorp, breached National Public Data and the FBI’s InfraGard, leaking sensitive information online. But this cybercriminal’s reign of terror has come to an end, as Brazil’s Polícia Federal recently arrested USDoD in “Operation Data Breach.”
USDoD’s Infamous Data Breaches
USDoD gained notoriety for his high-profile data breaches, often stealing data and leaking it on hacking forums while taunting his victims. His breaches include the FBI’s InfraGard, a threat information sharing portal, and National Public Data, where the personal data and social security numbers of hundreds of millions of US citizens were leaked online.
However, things took a turn for the worse for USDoD when he targeted cybersecurity firm CrowdStrike and leaked the company’s internal threat actor list.
How USDoD Was Caught
After leaking CrowdStrike’s list, Brazilian publisher Techmundo received an anonymous report created by CrowdStrike that allegedly identified, or doxed, the threat actor, revealing he was a 33-year-old Brazilian named Luan BG. Strangely, USDoD confirmed that CrowdStrike’s information was accurate in an interview with HackRead and said he was currently living in Brazil.
With this information, Brazil’s Polícia Federal (PF) announced his arrest in Belo Horizonte/MG. “The Federal Police launched Operation Data Breach on Wednesday (16/10), with the aim of investigating invasions of the systems of the Federal Police and other international institutions,” reads the PF’s press release.
The Importance of Cybersecurity
This arrest serves as a reminder of the importance of cybersecurity. As individuals and businesses, we must stay vigilant and proactive in protecting our sensitive data. But you don’t have to navigate the world of cybersecurity alone.
Our IT Services team is here to help you protect your data and ensure your digital safety. From implementing robust security measures to providing guidance on best practices, we’ll work with you to keep your information secure.
Stay Informed and Stay Safe
Knowledge is power, and staying informed about the latest cybersecurity threats and best practices is the first step in keeping your data safe. We encourage you to reach out to our team and keep coming back to learn more about how to protect yourself and your business from cybercriminals.
Malware
Cisco Probes Intrusion as Stolen Data Emerges for Sale on Cybercriminal Platform
Cisco is investigating a potential breach after a hacker claimed to have stolen 200GB of sensitive data. The company is working to determine the authenticity of the claim and assess any potential impacts on its customers. Protect your network with Cisco’s integrated security solutions and stay informed with the latest cybersecurity updates.

Recently, we received information that Cisco, a leading IT company, is investigating a possible data breach after a threat actor claimed to have stolen sensitive data and put it up for sale on a hacking forum. Don’t worry, we’ve got you covered with the latest updates on this situation.
What’s going on with Cisco?
Cisco confirmed that they are looking into these claims and have launched an investigation to assess the situation. A Cisco spokesperson stated, “We are aware of reports that an actor is alleging to have gained access to certain Cisco-related files.” The investigation is still ongoing.
This all started when a notorious threat actor going by the name “IntelBroker” claimed that they, along with two accomplices called “EnergyWeaponUser” and “zjj,” had breached Cisco on October 6, 2024, and made off with a significant amount of developer data from the company. The stolen data apparently includes GitHub projects, GitLab projects, SonarQube projects, source code, hardcoded credentials, customer documents, and much more.
What has been leaked?
IntelBroker shared samples of the alleged stolen data, which includes a database, customer information, various customer documentation, and screenshots of customer management portals. However, they did not provide any details about how they obtained the data.
It’s worth noting that back in June, IntelBroker was involved in selling or leaking data from several other companies, such as T-Mobile, AMD, and Apple. Those attacks were believed to have been carried out by targeting a third-party managed services provider for DevOps and software development. It’s not clear yet whether the Cisco breach is related to these previous incidents.
What’s the current status of the investigation?
As of now, Cisco is continuing to investigate the reports and has engaged law enforcement to assist in their efforts. So far, they have found no evidence of a breach in their systems. If any confidential customer information is confirmed to have been obtained by the threat actor, Cisco has stated that they will notify the affected customers.
In conclusion, it’s essential to stay vigilant and keep up-to-date on the latest cybersecurity news and threats. You can trust us to provide you with the most recent information and help you navigate the ever-evolving world of cybersecurity. Don’t hesitate to contact us to learn more about how to protect your organization, and keep coming back for more updates on this and other cybersecurity topics.
Malware
Game Freak Confirms Massive Breach: Stolen Pokémon Data Exposed Online
Game Freak, the developer behind Pokémon, has confirmed a security breach after stolen data leaked online. The leaked data includes information on unreleased games, potentially impacting both the company and fans. Game Freak is working to address the situation and strengthen their security measures to prevent future incidents.

Imagine spending years of your life working on a top-secret project, only for it to be stolen and leaked online. That’s what happened to Game Freak, the Japanese video game developer behind the wildly popular Pokémon series, in August 2024. And now, we’re learning just how extensive the damage was.
A Digital Heist in the World of Pokémon
Game Freak has been at the forefront of the Pokémon gaming world since 1996, when they released Pokémon Red and Blue for the Nintendo Game Boy. Since then, they’ve produced countless titles for various Nintendo platforms, as well as for iOS and Android devices.
But in August, things took a turn for the worse. Screenshots of source code and development builds for upcoming Pokémon games started appearing on leak sites and channels like Discord, Reddit, and X. While Game Freak didn’t acknowledge the leak of the game data, they did confirm something even more concerning: the personal information of their workforce, contractors, and former employees was stolen in the cyberattack.
Damage Control and Apologies
In a machine-translated notice, Game Freak stated, “We deeply apologize for any inconvenience and concern this may have caused to all concerned parties.” They went on to explain that the leaked information included full names and company email addresses. While this doesn’t put people at risk for identity theft, it does leave them vulnerable to phishing and targeted brute-forcing attacks.
Game Freak is working to contact those affected by the incident individually, but they published the notice on their site because not everyone can be reached. On a positive note, it seems that Pokémon player data hasn’t been impacted. Game Freak has completed a detailed investigation of the breached servers and implemented security measures to prevent similar incidents in the future.
Not an Isolated Incident
Game Freak isn’t the only gaming company to fall victim to a cyberattack recently. Earlier this month, Canadian video game developer Red Barrels warned its community that an attack could cause delays on patches and additional content for existing Outlast games and upcoming titles. The Nitrogen ransomware group later claimed responsibility for the attack, boasting that they had stolen 1.8 TB of confidential data from Red Barrels.
As for the attack on Game Freak, no one has claimed responsibility yet. But the fact remains that this is a stark reminder of the vulnerability of even the most successful companies in the gaming industry.
What You Can Do to Help
As fans and consumers, it’s essential for us to stay informed and vigilant about cybersecurity. By keeping up-to-date with the latest news and best practices, we can help protect ourselves and the companies we love from these devastating cyberattacks.
But you don’t have to do it alone. Our IT Services team is here to help you navigate the ever-evolving landscape of cybersecurity. Don’t hesitate to contact us with any questions or concerns you might have. And remember to keep coming back for the latest information and advice on staying secure in the digital world.
-

 Malware1 year ago
Malware1 year agoFlagstar Bank’s Latest Data Breach: 800,000 Customers Impacted, Marking the Third Incident of 2021
-

 Malware1 year ago
Malware1 year agoBlackbaud: Taking Responsibility with a Landmark $49.5 Million Settlement for Devastating Ransomware Data Breach
-

 Data Protection Regulations11 months ago
Data Protection Regulations11 months agoTop Data Protection Officer Certification Courses Reviewed
-

 Data Protection Regulations11 months ago
Data Protection Regulations11 months agoTop 11 Data Protection Training Programs for Compliance
-

 Security Audits and Assessments11 months ago
Security Audits and Assessments11 months agoMastering Healthcare Data Security: 5 Essential Audit Tips
-

 Data Protection Regulations11 months ago
Data Protection Regulations11 months agoNavigating Data Protection Laws for Nonprofits
-

 Data Protection Regulations11 months ago
Data Protection Regulations11 months ago9 Best Insights: CCPA’s Influence on Data Security
-

 Security Audits and Assessments11 months ago
Security Audits and Assessments11 months agoHIPAA Security Risk Assessment: Essential Steps Checklist































